Now You See It

Who owns your data?
For agents and brokers, that question sits squarely at the confluence of regulations, renegotiated agency contracts, and public unease over how business monetizes consumer data.
The question also presents agents and brokers with immediate and long-term challenges.
The widely held view is that businesses that collect customer data own it, no matter where that information ultimately ends up. That view means agencies and brokerages retain substantial liability in the event databases are compromised, whether in a direct breach or as part of a process involving a vendor. This means third-party vendors could be using data in ways that place both brokers and their clients at risk.
“Data-privacy laws hold the data owner responsible,” says Arturo Perez-Reyes, cyber and technology leader and senior vice president at Hub International. “Additionally, data processors do not even need to notify in the event of an incident. As for the subcontractors of processors, they are not in privity with the owner, so courts find that there are neither contractual nor tort obligations.”
The risks of unfettered data sharing have come into greater focus over time through multiple events and actions rather than a single incident. Arguably, the first event was the 2013 breach at Target, in which the perpetrators backed their way into the company’s corporate network by compromising a third-party vendor, a refrigeration contractor. The breach exposed the personal and financial information of about 110 million customers and resulted in the theft of 11 gigabytes of data.
As breaches continued, regulators took notice, addressing first the need for transparency. The European General Data Protection Regulation, created in 2016, addresses the transfer of personal data outside the European Union and the European Economic Area and seeks to give more control to individuals over their personal data. The following year, the New York Department of Financial Services instituted new mandates, known as Cybersecurity Requirements for Financial Services Companies, for developing effective cyber-security programs and assessing and mitigating cyber-security risk.
The National Association of Insurance Commissioners’ Insurance Data Security Model Law, introduced in 2017, established data-security standards for both regulators and insurers, including for information-security programs and the investigation and reporting of cyber-security events. The law covers agents as well, phasing in requirements for compliance with the information-security programs and oversight of third-party service providers. To date, 14 states have adopted or introduced versions of the NAIC model law.
The California Consumer Privacy Act (CCPA) went into effect Jan. 1, 2020. Before the deadline, vendors scrambled to comply by announcing updates to their terms of service and privacy policies. Yet the law, designed to help consumers understand what information is collected and how it is used, contains loopholes. According to Mary Stone Ross, a former president of Californians for Consumer Privacy who wrote a first draft of the CCPA, companies can still collect data, photos and emails but must tell consumers when asked what they’re collecting and delete it when requested.
“Companies can still deny such a request for certain reasons—to complete a financial transaction or protect against fraud—and can’t legally sell the data if you tell them not to,” Ross says. “But if they sell it anyway, a consumer can’t sue.”
Questions Abound
With multiple regulations in play and clearly a lot of gray area, ensuring compliance can be a confusing and onerous task.
“The NAIC model is in its infancy, with only a handful signing on to it,” says Heather Steinmiller, managing director of claims and general counsel of Conner Strong & Buckelew. “There’s some market resistance to it to the extent states seem to deviate from it. If states adopt various versions, it becomes onerous if we must deal with 50 different versions. We are a regional broker with national presence, so compliance will be difficult if we are being required to vet every vendor under 50 different standards and they must vet us. That becomes a monstrous paper battle.”
Perez-Reyes points out liability uncertainties within the GDPR and the CCPA. “The situation regarding value-chain liabilities is unclear in both GDPR and CCPA,” he says. “Data owners are obligated to review data processors, but neither law discusses the risks or liabilities of sub-subprocessors. Construction is a good example of the problem. The liabilities exceed the contractual chain and the insurance policies of the owners. Courts have stuck to contracts. The solution might be adopting strict liability.”
Christie Corado, senior vice president and deputy general counsel at Truist Insurance Holdings, says her bank-owned firm considers the New York regulations the current “gold standard” as the most precise and effective in mitigating cyber-security risk.
Consumer angst is also fueling action. In a Pew Research Center survey issued last November, a whopping 81% of those surveyed said the potential risks they face because of data collection now outweigh the benefits. The study also reported that 79% of respondents are concerned about the way their data are being used by companies. Similarly, 79% said they are “not too or not at all confident” that companies will admit mistakes and take responsibility if they misuse or compromise personal information, and 69% report having this same lack of confidence that firms will use their personal information in ways in which they will be comfortable.
Steinmiller acknowledged consumers’ concerns and the response to it, adding that the degree of uneasiness depends on the industry.
“The life sciences have always been sensitive about data security,” she says. “In our industry, though, it is not yet top-of-mind, but that is changing quickly. If we asked a client for permission to aggregate their data for modeling and benchmarking, they’d likely answer no, but they might reconsider if we can spell out how the data would be used and the value they’d get from it. How do you protect data at rest? This is a topic that’s only now being discussed.”
Carrier Requirements
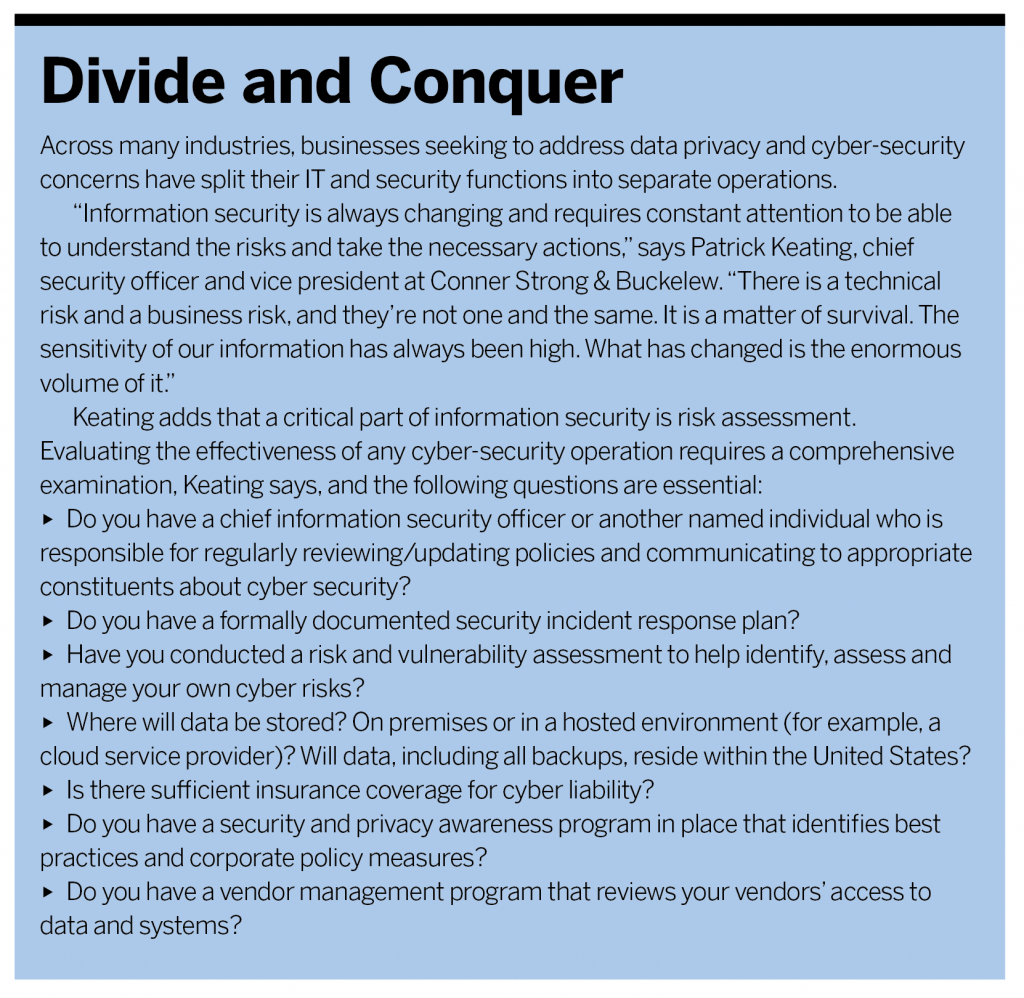
Insurers concerned with their own data security are now applying pressure on agencies and brokerages to strengthen their security efforts and are renegotiating contracts under three scenarios. The first, that of minimal action, involves the addition of several sentences calling on the firm to comply with all applicable state requirements and to follow industry standards on cyber security. A second approach, likely the most common, adds several new paragraphs and cites compliance with the New York regulations as best practice. The third and most aggressive model grants the insurer authority to audit an agency’s information-security system and make recommendations for improvements.
“We are in the midst of working with some carriers on the level of assessment they want from us,” says Brad Barron, deputy general counsel at Conner Strong & Buckelew. “The idea of many different risk-assessment audits that would each take a significant amount of time and probably not yield very much value for anyone is not very appealing. We think a better solution is for all involved to adopt a uniform questionnaire, with carriers adding in specific questions that may be unique to them. Brokers like us could then have on hand their responses to the uniform questionnaire, which would probably greatly increase the speed at which carriers get responses. This would address the insurer’s needs to obtain detail about brokers’ security programs quickly and allow brokers’ security personnel to focus on security and not a never-ending paper-pushing exercise with carriers.”
Steinmiller stresses that the risks are real, as is the need to limit exposure as much as possible, but she admits there’s still a lot of gray.
“We have the obligation to protect and the obligation to notify,” she says. “There are differing opinions as to who owns the data. It’s not entirely cut and dried.”
Joshua Motta, co-founder and CEO of cyber insurance and risk-management firm Coalition, underscores the urgency of the data-sharing issue.
“Brokers understand they must adapt technology to be competitive and efficient, not just on the premises but in the cloud,” Motta says. “They depend on third-party services. The threat is the destruction of data.”
Tom Wetzel is a contributing writer.